An unauthorized actor gained access to certain Vimeo user and customer data — a fact the company confirmed after forensic investigation traced the intrusion to a compromised third-party analytics vendor, Anodot. This incident has reignited concerns about supply chain vulnerabilities in cloud-based platforms, especially for businesses relying on SaaS tools to manage sensitive customer information.
The breach did not originate within Vimeo’s core infrastructure. Instead, attackers exploited credentials leaked from Anodot, a data monitoring service used by Vimeo to analyze system performance. Once inside, they accessed internal systems containing user data, primarily email addresses, hashed passwords, and limited customer account details.
This chain of events underscores a critical blind spot in modern digital security: the trust placed in external vendors. While Vimeo moved quickly to contain the damage, the ripple effects continue to unfold for users and enterprise clients alike.
How the Attack Unfolded: A Supply Chain Breakdown
The breach began not with a direct hack of Vimeo’s servers, but through Anodot, a cloud-based metrics and anomaly detection platform. On [publicly disclosed date], Anodot announced that an unauthorized third party had gained access to its systems through a compromised employee account. Credentials were stolen and later used to infiltrate customer environments — including Vimeo.
Vimeo confirmed that the attacker leveraged this access to view internal dashboards and logs that contained:
- User email addresses
- Encrypted (hashed) passwords
- Customer support tickets
- Limited billing information (e.g., last four digits of credit cards)
- IP addresses and device metadata
Notably, full payment details, video content, or private messages were not exposed — a significant containment win. Still, the accessed data is enough to fuel phishing campaigns, credential-stuffing attacks, and targeted social engineering.
Why this matters: Third-party vendors often have broad access to internal systems. When one fails, the domino effect can compromise dozens of downstream clients. Vimeo’s reliance on Anodot for performance monitoring created an attack vector outside its direct control.
What Vimeo’s Data Exposure Means for Users
While Vimeo insists no video content was accessed, the leaked metadata alone poses real risks. Here’s how different user types are affected:
Individual Creators Freelancers and independent content creators using Vimeo for portfolios or client pitches may now face: - Phishing attempts using personalized emails referencing their Vimeo activity - Credential stuffing on other platforms if they reused passwords - Impersonation risks if support tickets reveal project details or client names
Example: A filmmaker receives an email that reads, “We saw your project ‘Coastal Requiem’ on Vimeo and want to collaborate.” The message includes correct details from a private support ticket — a sure sign of data exposure.

Business and Enterprise Clients Teams using Vimeo for internal training, marketing, or secure video sharing face deeper consequences: - Reputational damage if clients learn their data passed through a breached system - Compliance risks under GDPR, CCPA, or HIPAA if personally identifiable information (PII) was exposed - IT audit failures due to reliance on a vendor with weak access controls
Workflow Tip: Immediately audit which team members accessed Vimeo during the breach window (typically 48–72 hours post-incident). Reset their passwords and enforce MFA.
Vimeo’s Response: Damage Control and System Hardening
Within 24 hours of detecting suspicious activity, Vimeo took the following actions:
- Revoked Anodot’s access to internal systems
- Rotated all API keys and service credentials
- Forced password resets for affected users
- Notified law enforcement and data protection authorities
- Launched third-party forensic investigation
The company also began notifying affected users via email, urging them to change passwords and enable two-factor authentication (2FA). Vimeo emphasized that passwords were hashed using bcrypt, making decryption extremely difficult — but not impossible with enough computing power.
Limitation in response: While Vimeo moved swiftly, the breach highlights a reactive rather than proactive stance. No public evidence suggests Vimeo conducted regular third-party risk assessments on Anodot prior to the incident — a common oversight in SaaS supply chains.
The Anodot Connection: A Weak Link in the Chain
Anodot, the Israeli-based analytics firm, serves over 200 enterprise clients, including Vimeo, Snapchat, and Coinbase. The breach occurred when an employee’s account was compromised, likely through phishing or credential theft.
Anodot admitted that the attacker accessed: - Internal Kubernetes clusters - Customer-facing dashboards - Log streams containing customer metadata
Despite claiming “no evidence” of data exfiltration, Vimeo and other clients could not assume safety — forcing emergency responses across the board.
Common Mistake: Many companies assume third-party vendors are “secure by default.” But Anodot lacked mandatory MFA for employee accounts at the time, a critical gap. This single oversight enabled the entire attack chain.
Best Practice: Always verify your vendor’s security posture. Ask for: - SOC 2 reports - MFA enforcement policies - Breach notification timelines - Data access logs and audit trails
If they can’t provide these, reconsider the partnership.
How to Protect Your Vimeo Account Now
Even if you weren’t directly notified, assume exposure if you used Vimeo during the incident window. Follow this checklist:
Immediate Actions
- ✅ Change your Vimeo password — Use a strong, unique combination
- ✅ Enable two-factor authentication (2FA) — Prefer authenticator apps over SMS
- ✅ Monitor email for phishing — Watch for messages referencing Vimeo projects or support tickets
- ✅ Check connected apps — Revoke access to unused third-party integrations
- ✅ Scan for credential reuse — Use a password manager to audit duplicates
For Teams and Admins - Audit user roles and permissions in Vimeo’s admin panel - Export and review recent login activity for anomalies - Conduct a vendor security review for all tools with system access - Implement session timeout policies for shared accounts
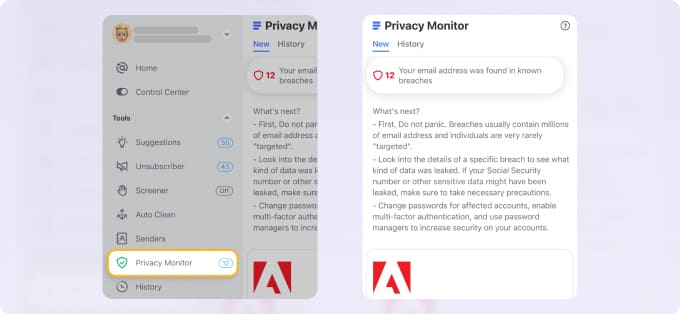
Pro Tip: Use tools like Have I Been Pwned or Bitwarden’s data breach scanner to check if your email appears in known leaks — including this one once it’s indexed.
Broader Lessons for SaaS Security
The Vimeo-Anodot incident isn’t isolated. It mirrors earlier supply chain attacks like SolarWinds and Codecov. What’s different now is the normalization of third-party access in cloud platforms.
Key Takeaways
- Trust is a vulnerability. Every vendor with system access expands your attack surface.
- Monitoring isn’t enough. Vimeo had visibility, but didn’t prevent misuse of legitimate credentials.
- Breach response starts before the breach. Companies with incident playbooks recover faster.
- Users are collateral damage. The burden of security often falls on individuals, not institutions.
Editorial Insight: We’ve built entire digital ecosystems on trust — between platforms, vendors, and users. But trust without verification is negligence. The next breach won’t come from a zero-day exploit. It’ll come from a forgotten API key or a vendor’s unpatched dashboard.
What Vimeo Should Do Next
To regain trust, Vimeo must go beyond notifications and password resets. Concrete steps include:
- Publishing a detailed post-incident report with timelines and root cause analysis
- Offering free credit monitoring or identity theft protection for enterprise clients
- Establishing a bug bounty program to incentivize external security research
- Requiring all third-party vendors to meet minimum security standards (e.g., MFA, audit logs)
- Enhancing user transparency with a security dashboard showing third-party access
Accountability isn’t just technical — it’s reputational. Vimeo has a chance to lead in SaaS security reform, or fade into another cautionary tale.
Closing: Assume Exposure, Act Now
An unauthorized actor accessed Vimeo user data — not through a flaw in Vimeo’s code, but through a trusted vendor’s failure. This incident proves that your security is only as strong as your weakest connection.
Don’t wait for a notification email. Change your password, enable 2FA, and audit your digital footprint. If you manage a team, treat this as a wake-up call to assess every tool touching your data.
Security isn’t a one-time fix. It’s a continuous process of verification, hardening, and vigilance. The Vimeo breach didn’t just compromise accounts — it exposed a systemic flaw in how we trust the digital supply chain. Fix your settings today. Tomorrow might be too late.
Frequently Asked Questions
Was my video content exposed in the Vimeo breach? No. Vimeo confirmed that the unauthorized actor did not access video files, private messages, or project details stored in user accounts.
Did the breach include passwords? Yes, but they were stored as hashed values using bcrypt. While not plaintext, attackers could attempt to crack weaker passwords over time.
Why was Anodot able to access Vimeo’s systems? Anodot provided analytics services to Vimeo, requiring access to internal performance data and logs — a common practice that created an indirect attack path.
Should I delete my Vimeo account? Not necessarily. If you take steps to secure your account (strong password, 2FA) and monitor for suspicious activity, your risk decreases significantly.
How can I check if my data was part of the breach? Vimeo is emailing affected users. You can also use breach monitoring tools like Have I Been Pwned and search by email.
Is Vimeo compliant with data protection laws after this incident? They are required to comply with GDPR, CCPA, and other regulations. Failure to implement adequate vendor controls could lead to fines, depending on investigation outcomes.
What should businesses do if they use Vimeo for internal communications? Conduct a risk assessment, notify stakeholders if PII was involved, and review all third-party integrations for similar vulnerabilities.
FAQ
What should you look for in Vimeo Data Breach: Unauthorized Access Linked to Anodot Leak? Focus on relevance, practical value, and how well the solution matches real user intent.
Is Vimeo Data Breach: Unauthorized Access Linked to Anodot Leak suitable for beginners? That depends on the workflow, but a clear step-by-step approach usually makes it easier to start.
How do you compare options around Vimeo Data Breach: Unauthorized Access Linked to Anodot Leak? Compare features, trust signals, limitations, pricing, and ease of implementation.
What mistakes should you avoid? Avoid generic choices, weak validation, and decisions based only on marketing claims.
What is the next best step? Shortlist the most relevant options, validate them quickly, and refine from real-world results.





:max_bytes(150000):strip_icc():focal(801x261:803x263)/Matthew-Lillard-paramount-event-102425-a13882f0fc524685bbb840985e4e9563.jpg)
